TL;DR
Google Just Set a Quantum Doomsday Clock — And It's at 2029 Google is scrambling to be quantum-proof by 2029 because a future supercomputer could crack today's encryption like a fortune cookie. The scary part isn't the timeline. It's that your data being harvested right now could be decrypted then. They're not stealing your secrets today. They're just... waiting.
A Greek Spyware Boss Just (Accidentally?) Ratted Out His Own Government The founder of Intellexa — the company behind the Predator spyware — is now hinting that the Greek government ordered hits on its own ministers, journalists, and military officials. This is either a bombshell or a very dramatic plea deal strategy. Possibly both.
Your Router Has No Password Protection. Neither Does Your Faith in TP-Link. TP-Link just patched a flaw that let hackers upload rogue firmware to your router without a password. No credentials. No phishing. Just... walk in. Change everything. Leave.
THIS WEEK’S TOP STORY
Microsoft 365 Is Being Used to Hack Microsoft 365…
And It's Already Hit Hundreds of Organizations Across 5 Countries…
Let's be crystal clear about what happened here.
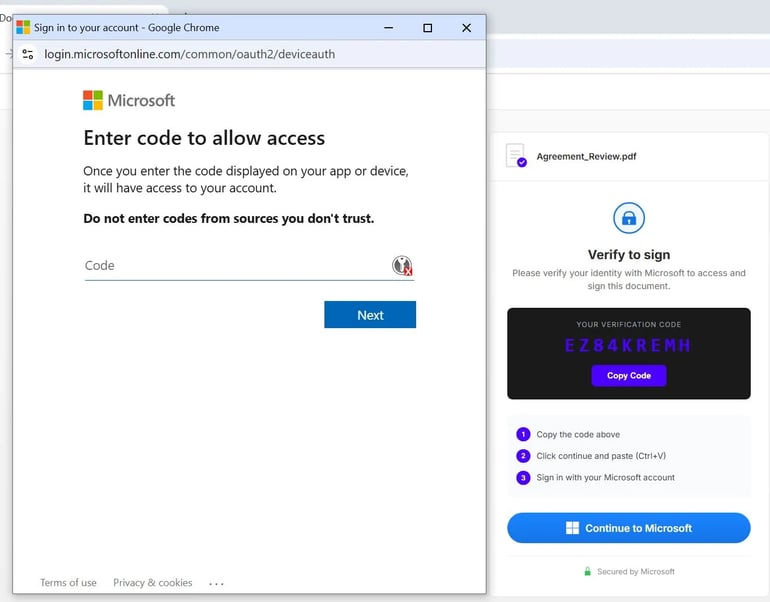
A sophisticated phishing campaign didn't brute force its way through your firewall. It didn't trick your intern into clicking a sketchy link. It didn't even break a sweat.
It used Microsoft's own legitimate login infrastructure to bypass Multi-Factor Authentication — the security feature that every IT department, every compliance officer, and every "have you tried turning on MFA?" tech support guy told you was the answer.
It wasn't.
The attack leverages Device Code Authentication — a real, legitimate Microsoft 365 feature designed to help users log in on devices without keyboards, like smart TVs. Attackers send targets a phishing email that initiates a genuine Microsoft login flow. The victim authenticates. MFA fires. They approve it.
And just like that, the attacker has a fully authenticated session token. No password stolen. No MFA code intercepted. The victim literally handed over the keys by doing everything right.
Hundreds of organizations across the US, Europe, Australia, Asia and the Middle East have already been hit. Energy companies. Healthcare. Government agencies. The works.
Learn more: https://www.techrepublic.com/article/news-microsoft-365-phishing-bypasses-security-codes/
OUR TAKE
Here's the part that should keep every CISO in America staring at their ceiling at 3am:
The attack used no malware. Triggered no alerts. Exploited no unpatched vulnerability.
It exploited trust. Specifically, your users' trust in a legitimate Microsoft prompt that looked exactly like every other legitimate Microsoft prompt they've clicked through a thousand times before.
We've spent a decade telling people to turn on MFA like it was the great wall between us and chaos. And now attackers have found the door in that wall — and it was Microsoft's door, built by Microsoft, for legitimate Microsoft reasons.
So what do you do when the security feature is the vulnerability?
That's not a rhetorical question. Because right now, hundreds of IT teams are asking it in real time — after the breach.
The uncomfortable truth this week isn't that hackers are getting smarter, though they are.
It's that we keep building security architecture on the assumption that attackers will play by the rules of the system we designed.
They won't. They never did.
And while you're reading this, someone, somewhere, is approving a Microsoft login prompt on their phone and wondering why their TV needs access to their corporate email.
Headlines
March 27, 2026
Are you one of the 270 Million People Exposed? If you don’t know for sure, the answer is probably, “yes!”
March 27, 2026
Google is racing to go quantum-proof before a future supercomputer renders every password, signature, and encrypted message in human history readable. The clock is ticking. Literally.
March 27, 2026
The founder of Intellexa, the company behind Predator spyware, is pointing fingers directly at the Greek government for authorizing surveillance of its own ministers, journalists, and military officials.
Editorial
Your House Is On Fire… But You're Arguing About With The Firemen About The Thermostat

Giphy
Let me paint you a picture of your week.
A nation-state level iPhone exploit leaked onto the open internet like someone accidentally posted the nuclear codes to a public Slack channel. A convicted spyware executive is casually implicating his own government in a phone hacking operation that reads like a John le Carré novel if John le Carré had given up on subtlety. Google just quietly announced that the encryption protecting everything you've ever sent, stored, or signed has an expiration date… and they've penciled it in for 2029, which is uncomfortably soon.
And the biggest phishing campaign of the year didn't use malware.
It used Microsoft.
Take a breath.
Now consider this: while all of that was happening, the Senate was asking data centers for their power bills. David Sacks quietly exited his role as AI czar. A White House official gave a speech about letting states regulate AI "a little bit." The intelligence community announced it was building a framework to think about adopting AI.
A framework.
To think about it.
Here's what nobody in a position of power wants to say out loud:
We are losing. Badly. And we are responding with committees.
The adversaries targeting your infrastructure right now are not waiting for a framework. They are not scheduling a working group. They are not requesting comment periods or commissioning reports or delivering keynotes at conferences about the importance of taking this seriously.
They are inside your Microsoft 365 tenant right now, moving laterally through your network with a session token they obtained because your employee did everything — everything — correctly.
That's not a user error story. That's a systemic failure story. And we keep telling it like it's the former because the latter is too uncomfortable to sit with.
Let's talk about quantum for a second, because I think we're not being honest about what Google's 2029 deadline actually means.
It means that everything being encrypted today — your emails, your financial transactions, your medical records, your government communications — is potentially being harvested right now by adversaries who are perfectly content to wait. They don't need to break the encryption today. They just need to collect the data and crack it later, when the computers are powerful enough.
It's called Harvest Now, Decrypt Later.
And it is happening.
Not theoretically. Not in a future threat model. Now.
While NIST talks about deprecating RSA algorithms by 2030, and the NCSC aligns its timeline accordingly, and Google heroically moves up its own deadline to 2029, someone in a server farm somewhere is sitting on an archive of your most sensitive communications, completely unbothered, watching the clock tick.
The house is not about to catch fire.
The house has been on fire for years. We just keep repainting the walls and calling it renovation.
And then there's the spyware story. The one that should be on every front page but somehow isn't loud enough.
The founder of Intellexa — the company that sold Predator spyware to governments — is now suggesting, with the casual energy of someone who has absolutely nothing left to lose, that the Greek government used it to hack its own senior ministers. Its own military officials. Its own journalists.
Read that again.
A government. Spying on itself. Using commercial spyware. Purchased legally. From a company that is now the subject of international sanctions.
And the executive is only talking because he got caught.
This isn't a Greek problem. This is a blueprint problem. Because Intellexa wasn't a rogue operation running out of a basement. It was a legitimate company selling legitimate products to legitimate governments who then did entirely illegitimate things with them.
The infrastructure of surveillance capitalism doesn't care about your political system. It just cares about the contract.
So where does that leave us?
We have a cybersecurity talent shortage so severe that CompTIA is out here suggesting tech support roles as an on-ramp to the industry — not as an insult, but as a genuine strategic necessity. We have AI being weaponized faster than we can defend against it. We have critical infrastructure secured by technology that was architected in a threat environment that no longer exists. We have governments buying power they shouldn't have from companies who shouldn't be selling it.
And we have a Senate committee asking data centers for their electricity bills.
I'm not here to tell you to panic.
Panic is useless. Panic doesn't patch your router. Panic doesn't migrate your cryptography. Panic doesn't build the workforce pipeline that this industry desperately needs or hold a government accountable for the spyware it bought with your tax dollars.
What I am telling you is this:
The gap between the speed of the threat and the speed of the response has never been wider.
And the people tasked with closing that gap are currently debating frameworks, commissioning reports, and waiting for the next conference to announce that they are very concerned and closely monitoring the situation.
Meanwhile, your Microsoft 365 session token is already gone.
Your iPhone vulnerability is already public.
Your encrypted data is already in someone else's archive.
And somewhere, a quantum computer is getting a little bit faster.
Every single day.
Other News From Around The Web
MFA Is Not Enough (Again)
Microsoft 365 phishing campaign bypasses MFA across 5 countries
A large-scale phishing campaign is exploiting legitimate Microsoft 365 login features to bypass MFA protections, impacting hundreds of organizations. The takeaway: identity security is now about session integrity, not just authentication.
Source: TechRepublic | Thu, Mar 26
Router takeover bug (no password required) patched by TP-Link
A high-severity vulnerability in TP-Link Archer routers allowed attackers to upload rogue firmware without authentication—another reminder that edge devices remain one of the weakest links.
Source: TechRepublic | Thu, Mar 26
Mobile & Exploit Ecosystem: Leaks, Spyware, and Scale
Advanced iPhone hacking tools (Coruna + DarkSword) leak online
A major leak of sophisticated exploit tooling could put millions of iPhones at risk, lowering the barrier for attackers and accelerating weaponization cycles.
Source: TechCrunch | Thu, Mar 26
Spyware vendors now rival nation-states in zero-day exploitation
Recent findings show commercial spyware suppliers are matching—or exceeding—nation-state actors in zero-day usage, signaling a major shift in who controls advanced cyber capabilities.
Source: Computer Weekly | (context from prior reporting trend)
Spyware scandal deepens: Greece government links alleged
A convicted spyware executive suggested government involvement in phone surveillance campaigns targeting officials, journalists, and opposition figures.
Source: TechCrunch | Wed, Mar 25
Cybersecurity Strategy & the Business Question
Is cybersecurity a growth sector—or just a cost center?
As spending rises, investors are questioning whether cybersecurity drives revenue or simply mitigates loss—a framing that could reshape budgets and expectations.
Source: Cybercrime Magazine | Wed, Mar 25
Who’s who in domain security (RSAC 2026)
A new CISO-focused report highlights leadership trends and evolving priorities across enterprise security teams.
Source: Cybercrime Magazine | Thu, Mar 26
Infrastructure, Policy & the Future of Encryption
Google targets 2029 for post-quantum cryptography migration
Google is accelerating its transition timeline, warning that “harvest now, decrypt later” attacks make today’s encryption vulnerable sooner than expected.
Source: Computer Weekly | Wed, Mar 25
Senators want answers on data center energy use
U.S. lawmakers are pushing for deeper reporting on how data centers consume electricity and impact the grid—bringing AI infrastructure into regulatory focus.
Source: TechCrunch | Thu, Mar 26
AI data centers face water backlash—new cooling solutions emerge
As scrutiny grows over water usage, alternative approaches like atmospheric water generation are being explored to make AI infrastructure more sustainable.
Source: TechRepublic | Thu, Mar 26
Government, AI & National Strategy
White House pushes “give and take” approach on AI regulation
Federal policy may allow states to regulate certain AI use cases (like child safety) while maintaining national standards—pointing toward a hybrid governance model.
Source: Nextgov | Thu, Mar 26
ODNI builds framework to expand AI adoption across intelligence agencies
A modernization push includes broader AI use and expanded threat hunting across intelligence community networks.
Source: Nextgov | Thu, Mar 26
UAE positions cybersecurity as core to national resilience
A coordinated, always-on cyber defense model emphasizes real-time monitoring, public-private coordination, and AI-driven security operations.
Source: Computer Weekly | Thu, Mar 26
David Sacks exits AI czar role
A shift in advisory leadership signals evolving influence structures in U.S. AI policy circles.
Source: TechCrunch | Thu, Mar 26
Enterprise IT & Cloud Strategy
Oracle bets big on bare metal cloud infrastructure
Oracle is doubling down on high-performance, low-virtualization cloud offerings, arguing that “bare metal” reduces both performance overhead and security risk.
Source: Computer Weekly | Thu, Mar 26
Workforce & Skills
Workforce pipelines become critical as talent shortages persist
A Trend Watch analysis highlights that hiring alone won’t solve tech talent gaps—structured development, certifications, and real-world experience are now essential.
Source: CompTIA (Video) | Thu, Mar 26
The Bottom Line
Your router has no password. Your iPhone (STILL) has a sword in it. Your encrypted data is being stockpiled by people with nothing but time and a quantum computer on order.
And the people responsible for stopping it are building frameworks.
Here's the only question that matters this week:
If a government can buy software to spy on itself, (and call it legal), what exactly are the rules?
Spoiler: There aren't any.
There's just money, motive, and a market that will happily service both.
Patch your systems. Question your governments. Read the stories that don't have catchy names.
And remember — the scariest hack of the week didn't use malware, didn't break a single rule, and didn't trigger a single alert.
It just asked nicely. And you said yes.